Most businesses buy cyber insurance expecting it to cover any cyber-related loss. Then a claim gets denied, and they learn the hard way that their policy had gaps they never knew existed.
Exclusions are not fine print designed to trick you. They exist because insurers need to define and price risk precisely. But if you do not understand what your policy excludes before a loss happens, that policy may not deliver what you paid for.
This guide covers the exclusions that appear most commonly in cyber insurance policies, what triggers them, and what questions to ask before you buy or renew.
Why Exclusions Matter More in Cyber Than in Other Lines
Most commercial lines of insurance cover a relatively well-understood, stable set of risks. Cyber is different. The threat landscape shifts constantly, attackers find new vectors, courts are still settling what legacy policy language means in modern contexts, and carriers are actively tightening exclusions in response to large-scale loss events.
That means a policy issued two years ago may read differently than one issued today. It also means the exclusions section deserves as much attention as the coverage grants.
The Exclusions You Are Most Likely to Encounter
1. Prior Known Incidents and Circumstances
This is the exclusion that catches the most unprepared buyers. If you knew about a security incident, breach, or vulnerability before your policy’s inception date and did not disclose it, your claim can be denied.
“Prior known” does not only mean a confirmed breach. Many policies extend this to circumstances that a reasonable person would recognize as likely to give rise to a claim. An open phishing investigation, a ransomware event you thought you contained, or a third-party notification about stolen credentials can all qualify as a “prior known circumstance” even if you had not yet filed a claim.
What to do: Before binding or renewing, conduct an honest internal review of any open security issues, incidents in the past 12 to 24 months, or third-party notifications you have received. Disclose proactively. Non-disclosure is the fastest path to a denied claim.
2. Failure to Maintain Security Controls
Carriers underwrite your policy based on the security posture you represent at application. If you attest that you have MFA enforced on all remote access and admin accounts, and a claim arises from an account that lacked MFA, coverage may be denied or significantly reduced.
This exclusion is enforced more aggressively than most buyers realize. Carriers increasingly use external scan data and post-loss forensics to verify that the controls you attested to were actually in place at the time of the incident. If there is a gap between what you represented and what forensics finds, the exclusion applies.
Common controls where misrepresentation issues arise include MFA, EDR deployment, RDP exposure, patch management, and immutable backup status.
What to do: Treat your cyber insurance application as a binding representation of your security posture, not a checkbox exercise. Document and verify controls before you attest to them. After binding, if a control changes or lapses, notify your broker. For guidance on the controls carriers currently require, see Cyber Insurance Requirements: The Minimum Controls Checklist.
3. Unencrypted or Unprotected Data
Many policies include exclusions or sublimits for losses involving data that was not adequately protected at the time of a breach. This most commonly appears as an exclusion for unencrypted personally identifiable information (PII) on lost or stolen devices, or data stored in plain text in environments that were accessible without proper controls.
Regulatory fines and notification costs in breach scenarios involving unprotected data can be significant, and if your policy excludes or limits coverage for those specific circumstances, you may be bearing a substantial portion of that cost yourself.
4. Social Engineering and Funds Transfer Fraud Sublimits
Social engineering and business email compromise (BEC) are among the most common cyber claim types, but they are frequently covered under a sublimit rather than the full policy limit. A policy with a $2 million limit may only provide $250,000 for a fraudulent wire transfer initiated by a BEC attack.
This is not technically an exclusion, but the practical effect is the same if the sublimit is insufficient for your exposure. BEC losses for mid-market companies can easily exceed seven figures, and a $250,000 sublimit provides false comfort.
What to do: Specifically ask your broker or underwriter what sublimit applies to social engineering, funds transfer fraud, and invoice manipulation. Negotiate the sublimit up if your business regularly processes large wire transfers or has high accounts payable exposure.
5. Infrastructure Failure and Utility Outages
Losses caused by power outages, telecommunications failures, or third-party infrastructure failures are often excluded unless your policy includes a specific contingent business interruption (CBI) endorsement covering non-attack-related outages.
The distinction matters because large-scale cloud provider outages, internet infrastructure disruptions, or utility failures can cause significant business interruption losses with no malicious actor involved. Standard cyber policies are primarily triggered by security events; infrastructure failure is often treated differently.
What to do: If your business is heavily dependent on a single cloud provider, SaaS platform, or third-party service, ask specifically about contingent business interruption coverage and whether it requires a security failure at the third party or covers any failure.
6. Bodily Injury and Property Damage
Traditional cyber policies exclude bodily injury and physical property damage arising from cyber events. This was largely theoretical for most businesses until critical infrastructure attacks became more frequent.
The Stryker attack earlier this year is a clear example of where this matters. An ECG transmission system used by paramedics was temporarily knocked offline. Medical device companies, industrial operations, and any organization whose systems touch physical outcomes face real exposure here that a standard cyber policy does not cover. This gap typically requires manuscript coverage or a specialized program.
For most SMBs and tech companies, this exclusion is not relevant to their primary risk. But it is worth understanding if your operations have any physical systems dependency. See The Stryker Attack: What It Means for Cyber Insurance Coverage for a detailed breakdown of how this plays out in practice.
7. Nation-State and Cyber War Exclusions
Since Lloyd’s Market Bulletin Y5381 took effect in March 2023, most standalone cyber policies have adopted explicit language excluding losses from state-backed cyber operations at warlike scale. The coverage question, practically speaking, is whether a given attack can be attributed to a state actor and whether the scale of that attack meets the threshold defined in your specific policy form.
For the vast majority of SMBs, this exclusion does not affect everyday ransomware, BEC, or data breach scenarios. Where it becomes relevant is in large-scale, geopolitically motivated incidents affecting many organizations simultaneously, such as the NotPetya-style events that triggered the original court battles over legacy war exclusion language.
The Handala attack on Stryker, attributed to an Iran-linked hacktivist group, is exactly the kind of event that puts this exclusion under a microscope. Attribution is contested, the wiper was destructive rather than financially motivated, and the scale was significant. That combination raises real questions about how different policy forms respond.
For a detailed breakdown of how nation-state exclusions are written, how attribution works, and what the NotPetya litigation settled and did not settle, see Nation-State Cyber Exclusions: What Buyers Need to Know.
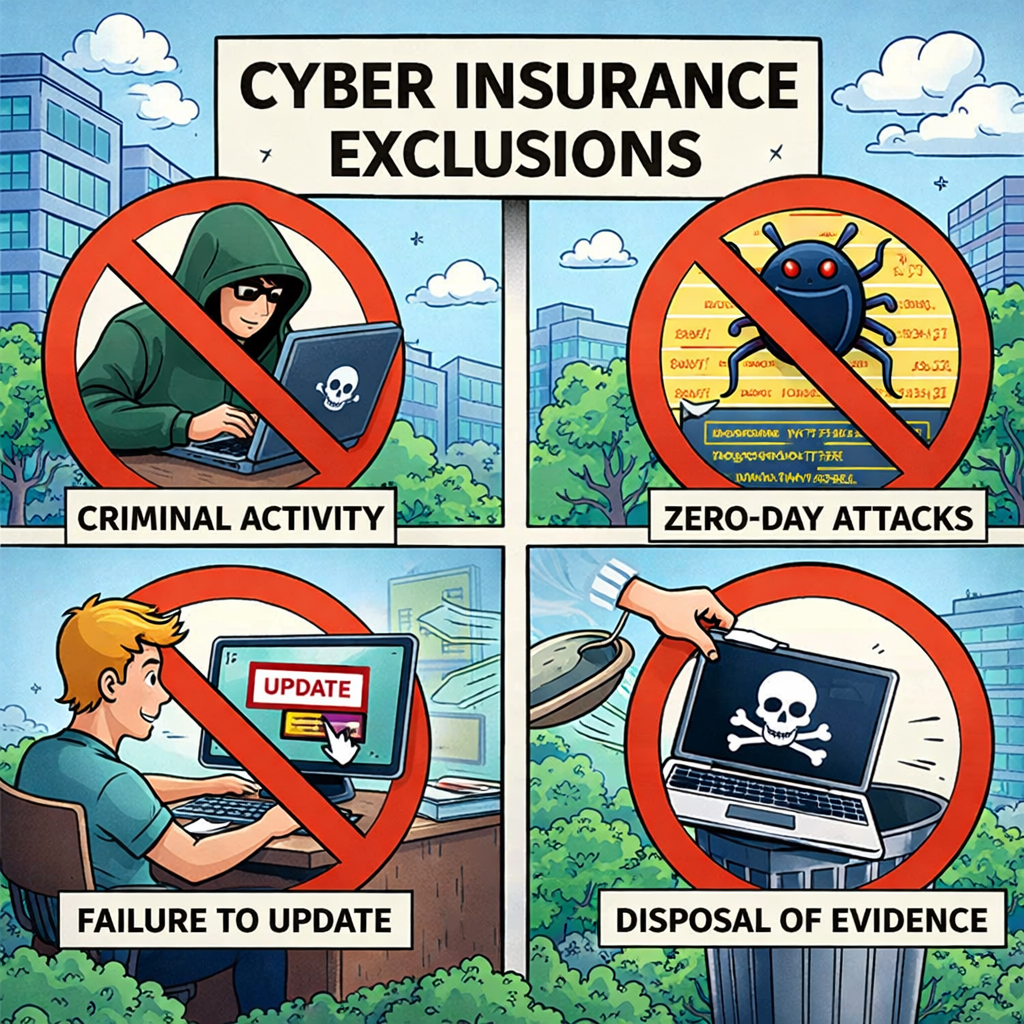
8. Intentional Acts and Criminal Conduct
Losses caused by the intentional acts of the policyholder or their principals are excluded. This is standard across all commercial lines and rarely creates surprises.
Where it can be more nuanced is in cases involving insider threats or employee fraud. If a trusted employee intentionally exfiltrates data or redirects funds, the exclusion may apply to their acts depending on how the policy defines “insured” and whether the employer had systems in place to detect and prevent the conduct. Separate crime coverage is often the right vehicle for employee dishonesty exposure.
9. Prior Litigation and Contractual Liability
Losses arising from disputes or claims that predate the policy period are excluded, as are losses arising purely from contractual obligations you assumed beyond what liability law would otherwise impose. This matters in contract negotiation: if you accept indemnification language in a vendor agreement that obligates you to cover breach costs regardless of fault, your cyber policy may not step in for the contractual portion of that obligation.
The Questions to Ask Before You Buy or Renew
Understanding exclusions before a loss is far more useful than understanding them after. Before binding or renewing a cyber policy, ask your broker these questions directly:
- What sublimit applies to social engineering and funds transfer fraud?
- Does the policy require a security event to trigger business interruption, or does infrastructure failure qualify?
- How is “prior known circumstance” defined, and what does the look-back period cover?
- Which nation-state/cyber war model clause does this policy use, and does it require attribution?
- Are controls representations warranties, and what happens if a control lapses post-bind?
- Is contingent business interruption included, and what triggers it?
If your broker cannot answer these questions, that is itself useful information.
How SeedPod Cyber Approaches This
Because SeedPod underwrites directly, we have a clear view of where coverage gaps occur at the application stage, not after a claim. Our underwriting process verifies controls before binding, which means the representations in your policy reflect your actual security posture. That matters at claim time when carriers look back at what you attested to.
If you want to understand exactly what your current policy covers and where the gaps are, contact SeedPod Cyber for a policy review. Getting that clarity before a loss is the entire point.
Related resources: